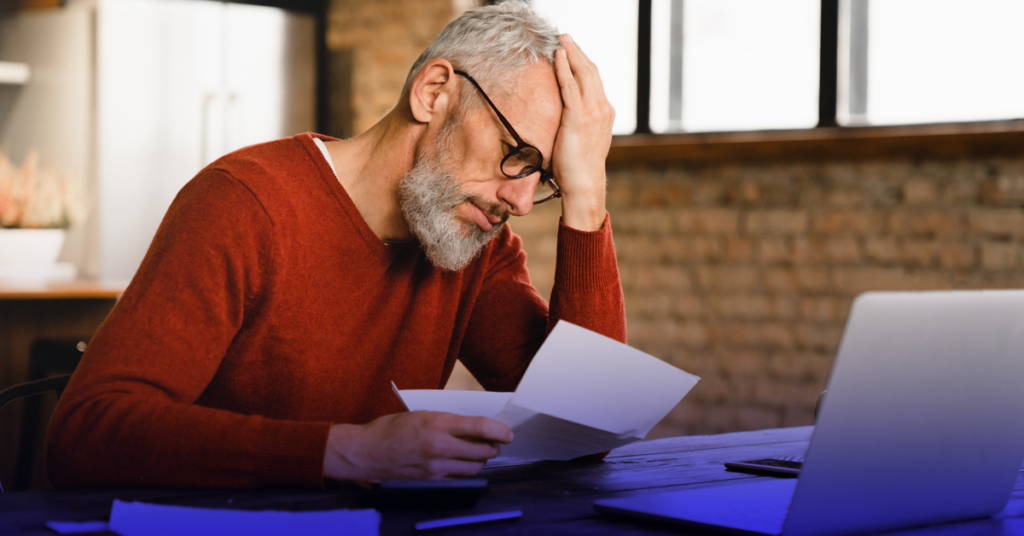
There are ways to lower the risk of being caught under the current wave of increased mail theft and check fraud.
Check Fraud Landscape
In the pre-digital era, check fraud schemes ruled the day. As millions of checks for utility bills, tax refunds, birthday gifts, and B2B payments made their way through the U.S. Postal Service, bad actors hunted for them like Easter eggs in mail rooms and mailboxes.
Although Automated Clearing House payments (ACH) emerged in the early 1970’s, the flow of paper checks did not decrease significantly until the late 1990’s when the technology to read and capture check images improved. With less eggs to find, bad actors more often looked to fill their baskets through other ways for the next decade or two–until 2020.
The COVID-19 pandemic presented new opportunities for an old method of theft and fraud. The supply of checks increased as pandemic relief efforts and unemployment assistance flooded the mail system. Postal Service blue collection boxes, personal mailboxes, and offices receiving mail were left vulnerable and unattended more often. And throughout, mail theft techniques were proliferated between bad actors and their recruits via social media and popular messaging apps.
Earlier this year, the Financial Crimes Enforcement Network (FinCEN)issued an alert after financial institutions reported more than 350,000 check fraud cases in 2021 (a 23% increase) followed by 680,000 reports, for a staggering 97% increase in 2022. With bad actors having now acquired the expertise to consistently profit from check fraud, those trends are not expected to significantly subside in 2023.
Vulnerabilities of Checks
A stolen check can be altered, deposited or cashed fraudulently, used to obtain personal or sensitive business information for larger identity theft schemes and, in many cases, all of the above.
Check washing is a method of altering a check by changing the payee name, changing the dollar amount, or both. Chemical solvents are used to remove the original ink from a targeted section of the paper check (or “scratched” using a sharp instrument, if pre-printed) and then new information is entered.
Deposit fraud occurs when someone poses as the payee to deposit the check, either remotely or in-person. Remote deposit requires an established bank account to receive the deposited check and some bad actors will go through the required steps to create (or take over) a bank account for this purpose.
Larger and more sophisticated check fraud schemes will enlist accomplices (known as “walkers”) to visit a bank to open an account and deposit the check, or direct them to check-cashing services to present the check and receive the funds. In cases where the payee line of the check has been washed and altered, the identity of the “walker” can be used as part of the scam. If the true payee name is on the check, fake identification documents are created while a new hair style, clothes, or other changes in appearance may also be necessary for the “walker” to successfully impersonate the true payee.
Since an in-person interaction will place the perpetrator at risk, organizers target vulnerable individuals willing to participate, or those who can be fooled into thinking they are part of a legitimate business arrangement or employment opportunity.
Stolen checks do not only put the intended payment dollars in harm’s way, but also the sensitive information of the intended recipient. A person or business name, address, or phone number, along with reference information that may be included in the memo line of a check can be used to extend the fraud to other opportunities, via identity theft.
Securing Provider Payments
For payers and providers seeking to avoid the perils associated with check fraud, taking advantage of Electronic Funds Transfer (EFT) to deliver and receive the payment is the most secure option. This method also enables an easier transition to, or enhancement of, the digital solutions available to streamline and optimize the overall claim and payment process.
Another option that eliminates the risks associated with a mailed check is a payment issued via virtual card. As a single-use method, there are also inherent protections that can limit potential fraud exposure and dollar amounts, as well as restrict use to predetermined service categories or specific provider credit card terminals.
Consolidate payments processing and member communications into a single platform. Payments moved to a single ecosystem can increase efficiencies, in effect reducing the “noise” that can leave an organization susceptible to bad actors. Look for solutions that dedicate hefty resources to process management, provider provisioning, bank account verification, fraud mitigation and compliance.
In the Meantime
If moving on from paper check payment is not possible (or during a transition to digital payments), there are ways to lower the risk involved and reduce the likelihood of being caught under the current wave of increased mail theft and check fraud:
- Ensure the security of where incoming or outgoing mail is placed for you or your business.
- Limit the receiving and/or processing of your mail to trusted individuals.
- Deposit checks as soon as possible, to avoid checks being misplaced or falling into the wrong hands.
- Destroy or secure checks that cleared or were deposited remotely; cancelled or expired checks can still be utilized by bad actors.
- Utilize Informed Delivery to know in advance what is expected to arrive in the mail and detect items that may have been stolen.
- Immediately report suspected or confirmed mail theft or check fraud, including to the United States Postal Inspector.
Zelis Fraud Protection
Whatever payment method is utilized by a payer or provider, all Zelis Payments Optimization solutions (including ZAPPSM, the Zelis Advanced Payments Platform) benefit from dedicated fraud prevention and detection teams using advanced tools and expansive industry knowledge to vigorously defend against fraud risk and ensure payment security.
To learn more about those protections, visit the ZAPP page or connect with us.